Malware analysis tools that are used to isolate and investigate malware as it is detected on a company’s IT assets, endpoints, and applications. They normally work by identifying malware and afterward moving infected resources or contaminated assets to an isolated environment. In this secure, sandboxed environment, security experts analyze the malware’s code and behaviors to study more about how it works, what it has done, and how to safeguard against it in the future.
Security groups and other IT staff engaged in incident response, risk analysis, and security operations may all utilize these tools. They gather information from malware that is detected and use it to support security and prevent similar malware from compromising their system by integrating it with their existing threat intelligence systems. They may also utilize the information gathered to examine larger portions of their IT systems to ensure the malware is not present elsewhere.
Numerous malware analysis solutions provide features of network sandboxing software for secure analysis. Not all network sandboxing tools have the same ability to automatically detect malware nor the tools necessary for in-depth forensic investigation.
- Intezer Analyze
- VirusTotal
- Comodo Antivirus
- Trellix Intelligent Sandbox
- Filewall
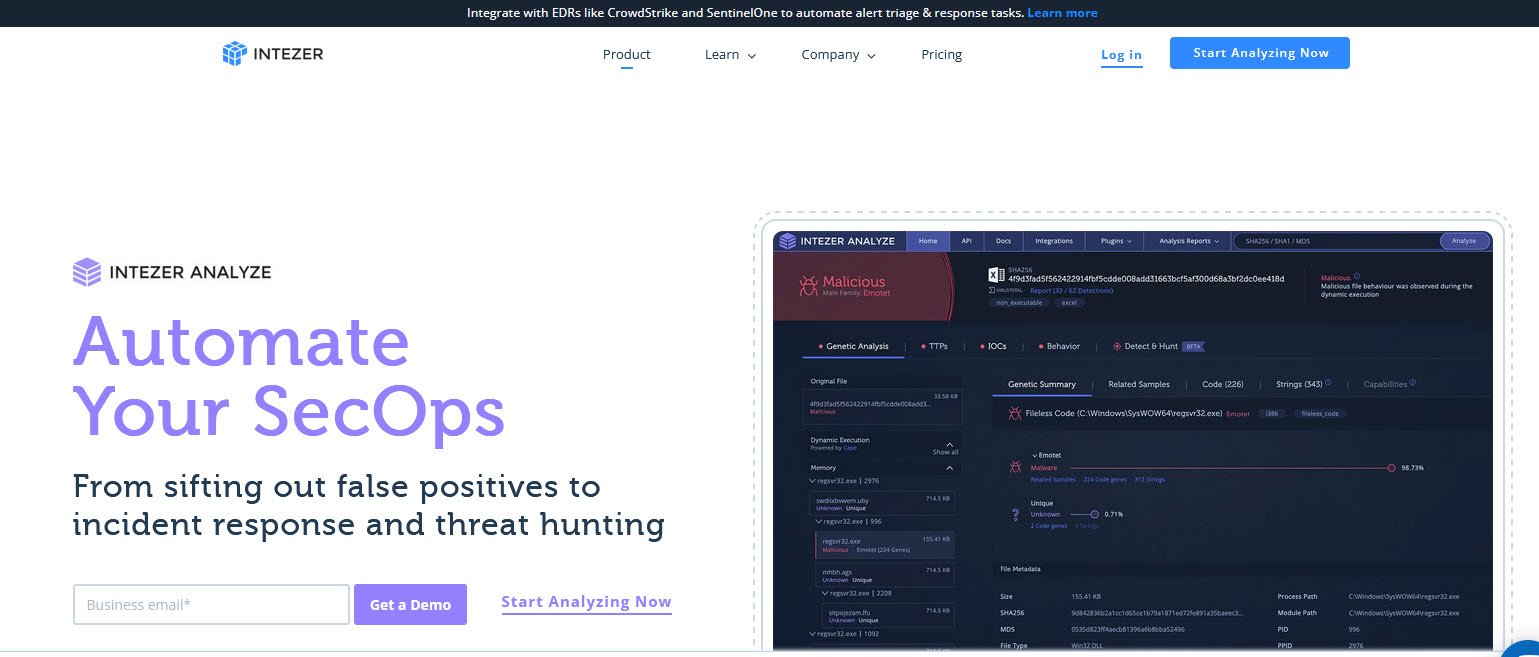
1. Intezer Analyze
Intezer automates alert triage, incident response and threat hunting by analyzing potential threats (such as URLs, files and endpoints) and automatically extracts IoCs/hunting rules—providing clear classification and better detection opportunities. You can easily integrate Intezer into SOC and IR teams workflows (EDR, SOAR, SIEM, etc.) to eliminate most false positives and reduce 90% of alert response time.
- Step 1 – Connect Alert Sources – Connect Intezer to your detection tools (EDR, SOAR, etc.) with an API key and/or install a plugin.
- Step 2 – Let Intezer Investigate Your Alerts – Intezer automatically ingests your alerts and analyzes any relevant artifacts (files, URLs, memory images).
- Step 3 – Your Alerts Get Triaged – Decrease false positives by 75%; You get clear recommended actions fast and IOCs for every alert.
2. VirusTotal
VirusTotal is a service that analyzes suspicious files and facilitates real-time detection of viruses, worms, trojans and malware content.
It also extract suspicious signals such as OLE VBA code streams in Office document macros, invalid cross reference tables in PDFs, packer details in Windows Executables, intrusion detection system alerts triggered in PCAPs, Exif metadata, authenticode signatures and a myriad of other properties.
You can use these properties as IoCs to hunt down badness in your network.

3. Comodo Antivirus
Get unbeatable protection from every type of malware with Comodo’s award-winning free Antivirus. Lightning fast cloud scanner blocks malware even if you don’t have the latest updates.
It also blocks ransomware and zero-day threats by locking them in a secure container where they cannot infect your computer.
Features –
- Default Deny Protection
- Prevention-based security
- Auto Sandbox Technology
- Secure Shopping
- Full strength, top notch virus detection and elimination
- Quarantine system to isolate suspicious files
- Personalized protection
- Spyware Scanning
- Cloud based Antivirus
- Cloud based Behavior Analysis
- Cloud based Whitelisting
- Game Mode
- Application Control
- One-click scanning
- Easy and user-friendly interface
- Real-time access to updated virus definitions

4. Trellix Intelligent Sandbox
Trellix Intelligent Sandbox enables your organization to detect advanced, evasive malware and convert threat information into immediate action and protection. Unlike traditional sandboxes, it includes additional inspection capabilities that broaden detection and expose evasive threats.
You can easily share threat intelligence across your entire infrastructure—including multi-vendor ecosystems—to reduce time from threat encounter to containment.

5. Filewall
odix – a market leader in Enterprise CDR (Content Disarm and Reconstruction), is now offering FileWall, a native cybersecurity application for Microsoft Office 365 mailboxes for SMEs.
FileWall is designed to run in conjunction with existing Microsoft security solutions such as EOP and Windows Defender (Formerly ATP), ensuring complete prevention against unknown attacks delivered via email attachments. FileWall™ doesn’t harm/change any of Microsoft sender related security capabilities.
odix offers malware prevention solutions using Deep Files Analysis technology to effectively protect cloud business applications from File-Based Attacks.
Any program running on your machine will require a certain amount of processing power to work, which can affect your computer’s overall performance. If an antivirus program is just running in the background, it shouldn’t really have any effect on your computer’s performance.
There are hundreds of malware analysis solutions available. We investigated 5 popular solutions often considered the software of choice by cybersecurity experts. Of critical importance was the ease of use with all providers, making it something every consumer could navigate and use.



Pingback: Top 6 Cybersecurity Tools Compared - Norton, McAfee, Bitdefender & More - TopatTop.com