Posted inTop 5
Top 5 Cloud Security Posture Management (CSPM) Softwares
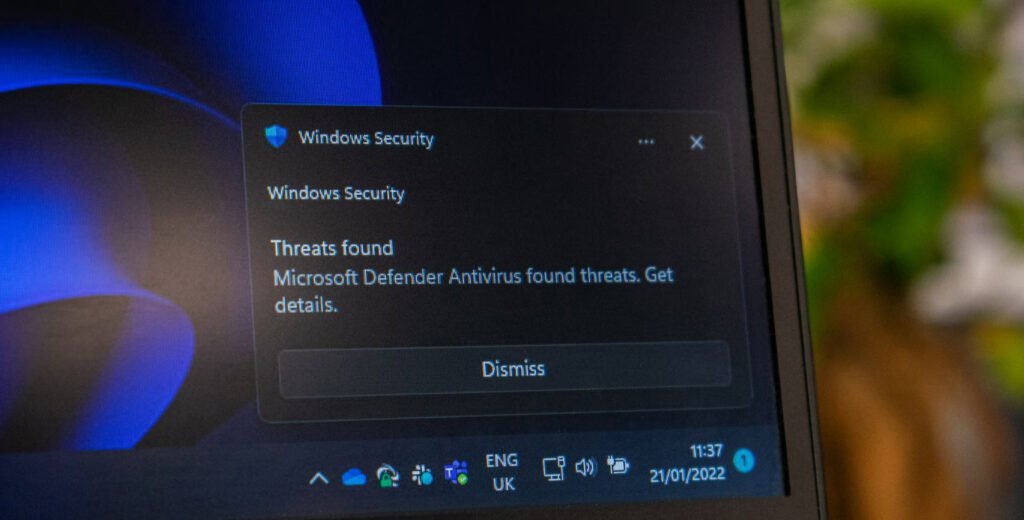
The Cloud Security Posture Management (CSPM) tool automates managing cloud security across a variety of infrastructure, including: Instant computer infrastructure that is delivered and managed via the internet is known…