Information stored within cloud-based (SaaS) applications is secured using cloud file security software. These solutions work together with cloud-based programmes used for file sharing and storage.
Cloud file security solutions are frequently used by businesses to detect files that contain confidential or privileged information. Companies can restrict access to the files, track file sharing history, and bar unauthorized parties from accessing them once these files are correctly tagged.
- BetterCloud
- Avanan Cloud Email Security
- Tresorit
- Duo Security
- DiskStation
- ESET PROTECT Advanced
- Redstor Backup for Microsoft 365
- Avast Business Antivirus Pro Plus
- Virtru
- Harmony Email & Office
1. BetterCloud
The market leader in SaaS Operations, BetterCloud enables IT professionals to enhance the employee experience, increase operational effectiveness, and centralise data protection. Numerous forward-thinking businesses, like Walmart, Oscar Health, and Square, now rely on BetterCloud to automate procedures and rules across their portfolio of cloud applications thanks to the company’s growing network of SaaS connections.
2. Avanan Cloud Email Security
Avanan, a CheckPoint Company, stops sophisticated attacks that get past both standard and cutting-edge security measures. Full-suite protection for cloud collaboration products like Office 365, G-Suite, and Slack is made possible by its transparent, multi-layer security. The technology deploys through API in a single click and guards against business email compromise as well as phishing, malware, data loss, account takeover, and shadow IT.
The necessity for numerous solutions to protect the complete cloud collaboration suite is replaced with Avanan.
3. Tresorit
Tresorit is a Swiss, end-to-end encrypted, zero-knowledge content collaboration platform designed to safeguard the digital valuables of individuals and organizations with the highest classification in the cloud. Tresorit does not have access to users’ files, in contrast to other public cloud providers, guaranteeing full secrecy.
4. Duo Security
Users, data, and applications are safeguarded by Duo Security’s seamless Trusted Access platform against hostile hackers and data breaches.
Our goal is to keep your mission safe. So that you can concentrate on what is crucial, Duo Security makes security painless. Security issues are addressed by our scalable, cloud-based Trusted Access technology before they become a problem. We accomplish this by confirming your users’ identities and the functionality of their devices before they connect to the apps you want them to use.
5. DiskStation
Users can manage digital assets across many places with the use of the web-based operating system called DiskStation Manager, which is made for Synology network attached storage (NAS) machines. Full-text search, metadata management, data backup, and virtualization are among the features.
Every Synology NAS comes with DiskStation Manager (DSM), an easy-to-use web-based operating system that is intended to help you manage your digital assets both at home and at work.
6. ESET PROTECT Advanced
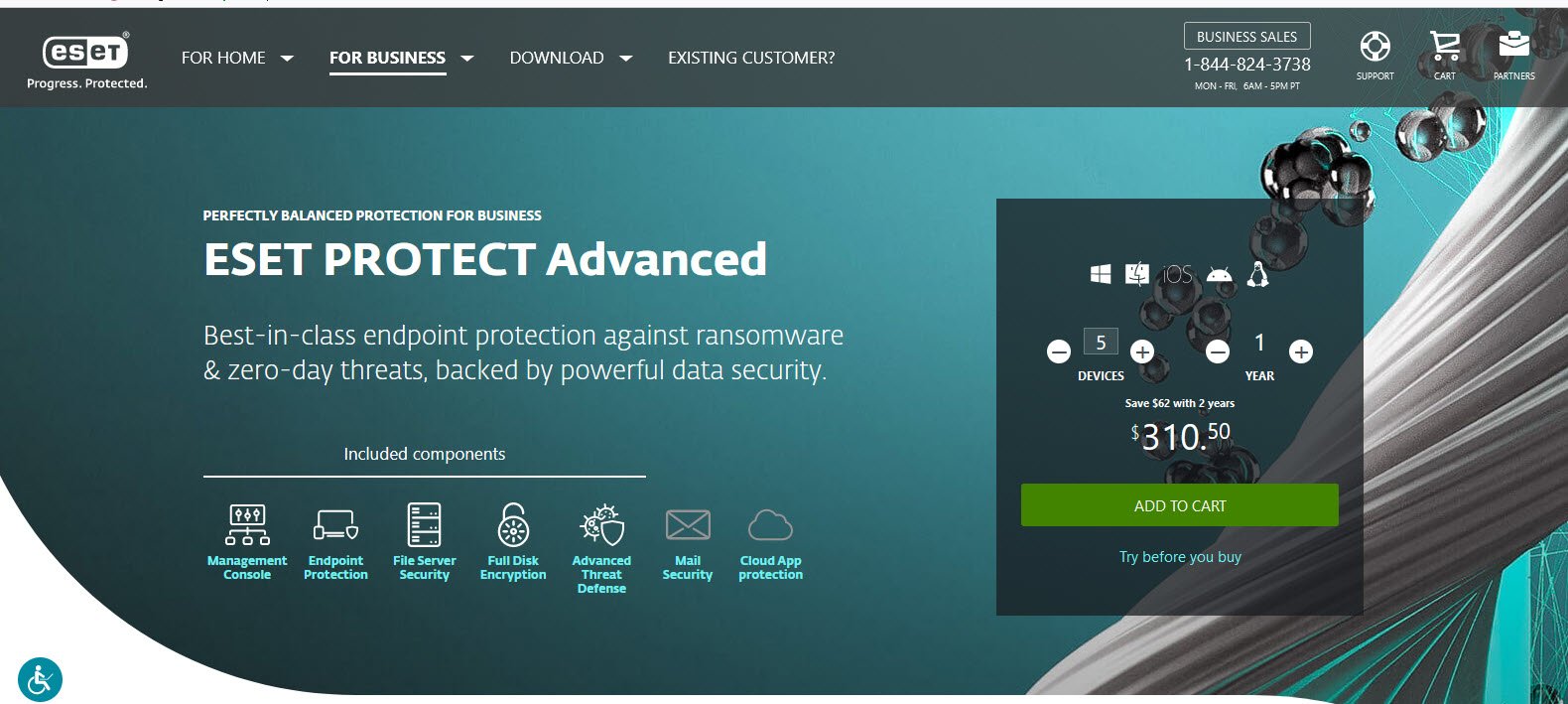
ESET has been creating market-leading IT security software and services for more than 30 years to defend consumers, businesses, and critical infrastructure from increasingly sophisticated online threats. ESET’s high-performing, simple-to-use solutions discreetly protect and monitor 24/7, updating defences in real time to keep users safe and businesses operating without interruption.
They cover endpoint and mobile security, endpoint detection and response, encryption, and multifactor authentication. A corporation that provides IT security services and facilitates safe technology use must adapt to threats as they arise. This is supported by ESET’s R&D facilities around the world, which are working to advance our shared future.
7. Redstor Backup for Microsoft 365
Market-leading Microsoft 365 coverage, including full protection for SharePoint, OneDrive, Email, Teams, OneNote, and even Class and Staff Notebooks, is included in Redstor’s Microsoft 365 backup solution.
The Redstor app incorporates AI to highlight 365 data threats, protect users from malware, including blocking ransomware recovery, and make continual improvements based on community-shared insights.
8. Avast Business Antivirus Pro Plus
A robust endpoint security solution supplemented with Windows Server-specific capabilities will help you stay ahead of cyber threats and secure all company devices. Gain from improved security in teamwork settings, simple management from a single central platform, and more.
9. Virtru
Virtru, a leader in data security and privacy, provides businesses with adaptable, end-to-end data encryption solutions that safeguard videos, emails, files, databases, and other types of data.
The tools from Virtru are simple to use and interface with business software like Salesforce, SAP, and Zendesk as well as Gmail, Outlook, and Google Workspace. Additionally, enterprises are able to comply with regulations like GDPR, HIPAA, ITAR, and CJIS thanks to capabilities like access restrictions, key management, DLP rules, and persistent audit.
10. Harmony Email & Office

The world’s most potent threat intelligence and more than 60 threat prevention engines power Harmony Email & Office, a product of Check Point Infinity. The only email security solution that uses technologies with a proven 99.91% catch rate. SaaS applications and cloud-based email are shielded from targeted attacks thanks to Check Point Harmony Email & Office.




Pingback: The Best Five Financial Analysis Software - TopatTop.com