With the help of a platform made for this purpose, it is easier to protect servers, cloud infrastructure, and VMs from online attacks. To qualify for inclusion in the Cloud Workload Protection Platforms category, a product must:
– Protect cloud infrastructure and virtual machines.
– Support container-based application security.
– Monitor and protect public, private, or hybrid-cloud environments.
- CloudGuard Network Security (IaaS)
- Lacework
- Trend Micro Hybrid Cloud Security Solution
- Google Cloud Platform Security Overview
- Trend Micro Deep Security
- Orca Security
- CloudGuard Posture Management (Dome9)
- InsightVM (Nexpose)
- Armor Anywhere
- Sysdig Platform
1. CloudGuard Network Security (IaaS)
In order to safeguard assets stored in the cloud from even the most sophisticated types of attack, CloudGuard Network Security (IaaS) was developed.
2. Lacework
Lacework was made to be a security solution for the cloud that is based on data. Polygraph-driven Lacework Cloud Security Platform automates cloud security at scale to help our clients move forward quickly without sacrificing security.
There is no other security platform like Lacework, which can collect, analyze, and accurately correlate data from an organization’s AWS, Azure, and GCP environments and then boil this data down to the few security events that really matter. Kubernetes is a container orchestration platform that is free to use. It is used to manage software that comes in packages.
Lacework has clients all over the world, and they depend on the company to help them grow their businesses financially, get new products to market faster, and improve their security by combining different security measures.
3. Trend Micro Hybrid Cloud Security Solution
Using Trend Micro Cloud One, a security services platform made for cloud architects, you can easily and simply protect your cloud infrastructure. This platform offers the most security features at a reasonable price in the cloud security industry, and it does this for all of the major cloud providers.
Trend Micro Cloud One can give your cloud environment a very high level of security because it takes into account all of your cloud projects and goals as a whole. So, it’s easy for your business to take advantage of the cloud’s many benefits and time-savings.
If you choose Trend Micro Cloud One, you’ll be able to adapt to your current problems and be ready to try new things as your cloud services grow. Having access to both of these tools can help you meet your company’s needs better. On the Trend Micro Cloud One platform, different services have been made to meet the needs of different kinds of cloud security.
4. Google Cloud Platform Security Overview
The Cloud Platform Security Overview says that top professionals keep a close eye on the security of information, applications, and networks.
5. Trend Micro Deep Security

Trend Micro Deep Security was made because security management needed to be made easier and more visible in all deployment scenarios, whether they were on-premises, in the cloud, or a mix of the two.
6. Orca Security

Orca Security offers instant-on security and compliance for AWS, Azure, and Google Cloud Platform. It is widely seen as the leader in cloud security innovation. This is done without agents or sidecars, which could lead to coverage gaps, alert fatigue, and higher operational costs.
Using a unified CNAPP platform for workload and data protection, cloud security posture management, vulnerability management, identity management, and compliance management may give your team superpowers while also making cloud security operations easier.
Orca Security makes a graph that includes not only trust but also every cloud asset, piece of software, and connection. When putting a score on each risk in this graph, the severity of the security flaw, how easy it is to get to, and how it will affect the company are all taken into account. This way, you won’t have to worry about the hundreds of useless security alerts that keep popping up on your phone. Instead, you’ll be able to focus on the things that need it the most.
7. CloudGuard Posture Management (Dome9)

Organizations can use CloudGuard Posture Management to learn about their current security posture, find misconfigurations, model and actively enforce security best practices, and more to protect themselves against cloud-based identity theft and data loss (Dome9).
8. InsightVM (Nexpose)
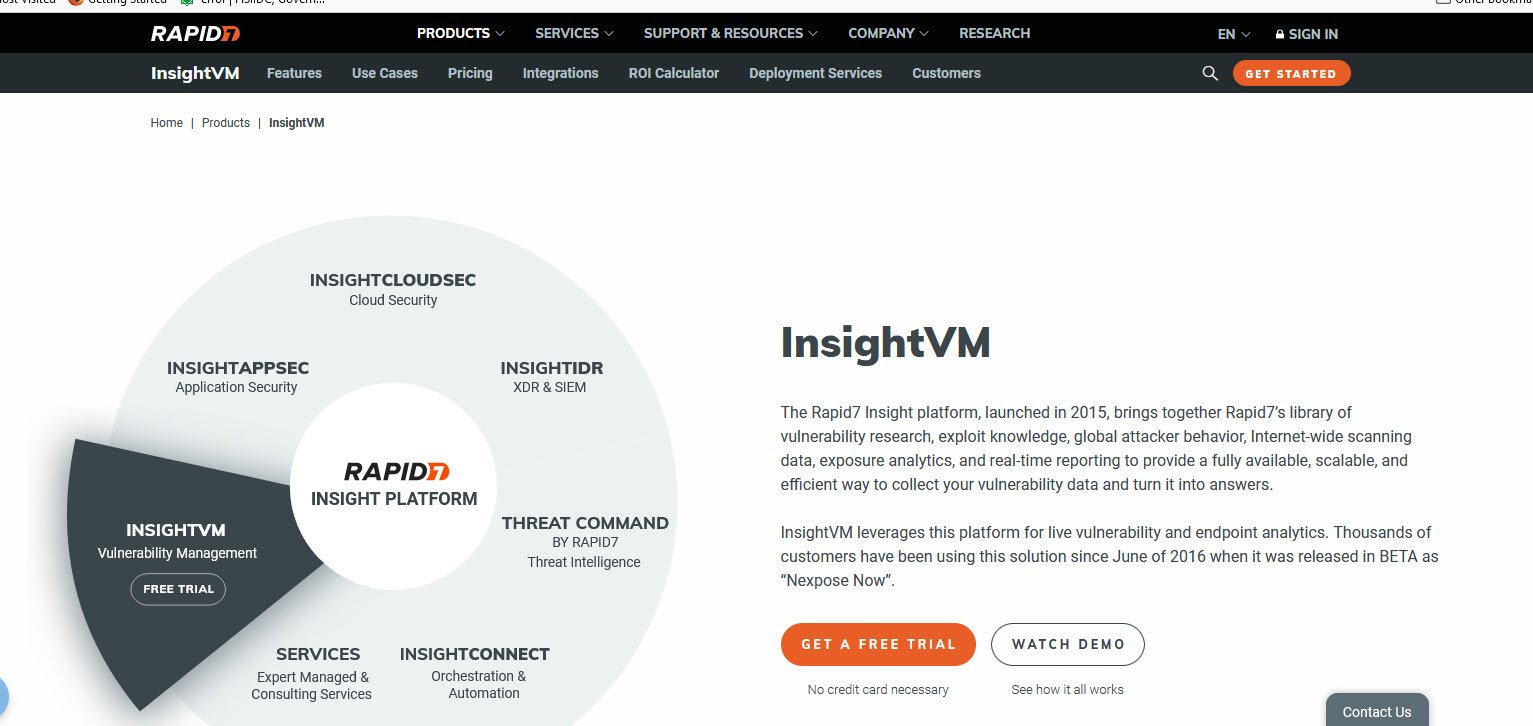
The Rapid7 InsightVM vulnerability management tool is often used to protect systems from security flaws that could cause problems. This service contributes to a higher level of security in a number of ways.
Some of these are a better understanding of risks, more clarity for many departments, and a more accurate way to track progress. Security teams are in charge of finding security holes and fixing them, as long as they keep technical teams informed and work well together.
9. Armor Anywhere
Armor has become the standard way to protect data in the cloud. We make cybersecurity and compliance easy for managed service providers (MSPs) and the clients they serve across endpoints, networks, servers, and the cloud.
Armor gives businesses a huge amount of information about threats and helps them respond to them quickly and effectively. Armor was designed and made by IBM. Armor works with the best managed security service providers in the industry to protect more than 1,500 clients in more than 40 countries (MSPs).
10. Sysdig Platform

A business that makes money At the moment, Sysdig is in charge of figuring out what steps need to be taken to keep cloud and container infrastructure safe. The company’s development of Falco and Sysdig as open source standards and key building blocks for the Sysdig platform makes it a leader in detecting and responding to cloud-native runtime threats.
Teams can use the platform to find threats and deal with them, manage cloud settings, permissions, and compliance requirements, and put software vulnerabilities in order of importance. Teams get a bird’s-eye view of the risk from the beginning to the end, so they don’t have to guess or worry about hidden dangers.
This is true for any service, whether it’s a cloud service or a platform for managing containers. Many of the most successful and cutting-edge businesses in the world use Sysdig as their business intelligence platform of choice.



